
Essential Tech Blogs Every Software Engineer Should Follow
Tech Company Blogs Netflix Tech Blog Google Developers Blog Amazon Web Services (AWS) Blog Uber Engineering Blog Stripe Engineering Blog Airbnb Engineering Blog Meta Engineering Blog...

Tech Company Blogs Netflix Tech Blog Google Developers Blog Amazon Web Services (AWS) Blog Uber Engineering Blog Stripe Engineering Blog Airbnb Engineering Blog Meta Engineering Blog...
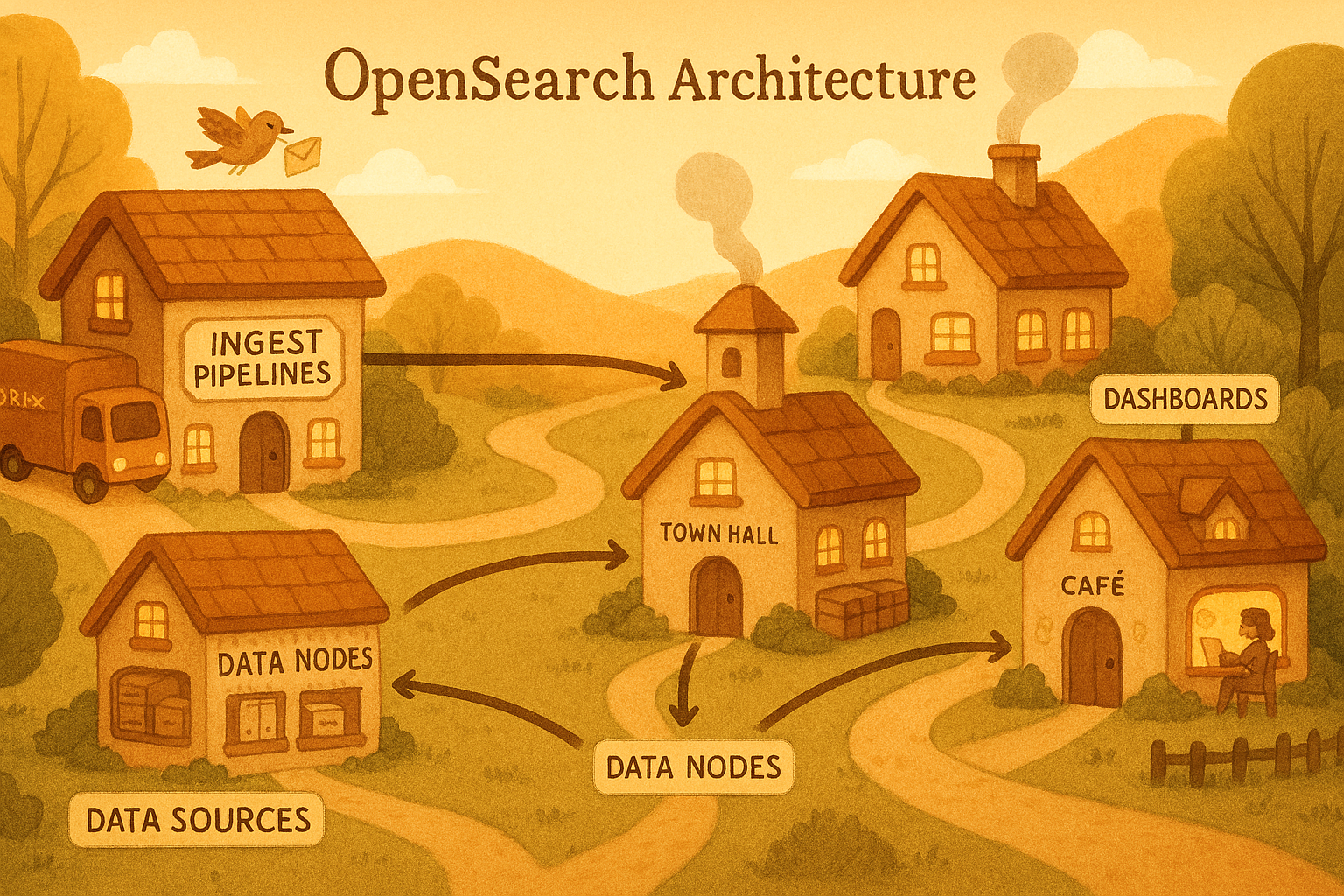
In the previous three articles, we covered the architecture of OpenSearch and Fluent Bit, how to set up a high-throughput logging pipeline, and how to optimize for ingestion performance. In this fi...
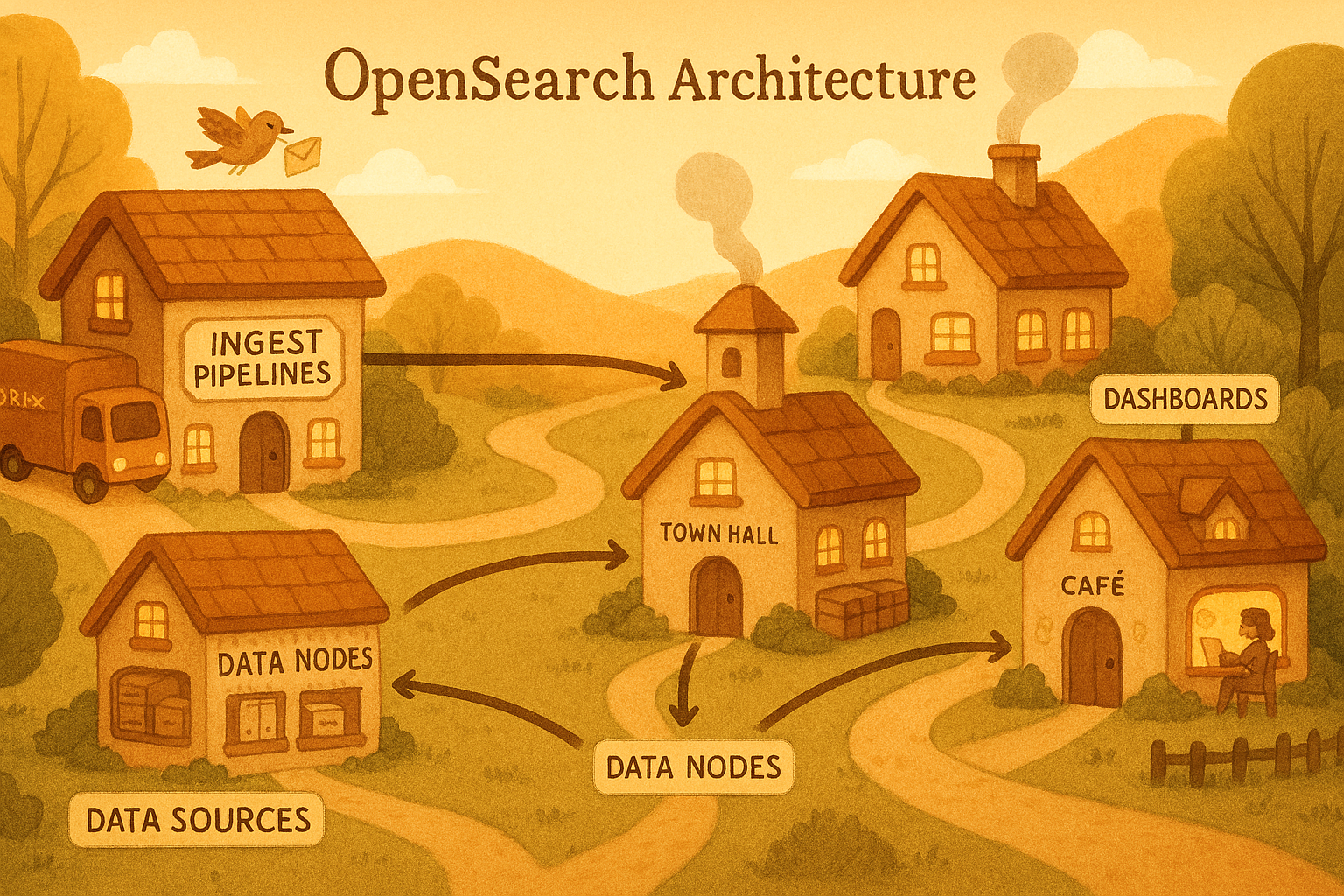
In Part 2 we covered Amazon OpenSearch Ingestion, time-based index strategy, ISM lifecycle policies, and network optimisation for high log volume. This post completes the series. We will use OpenS...
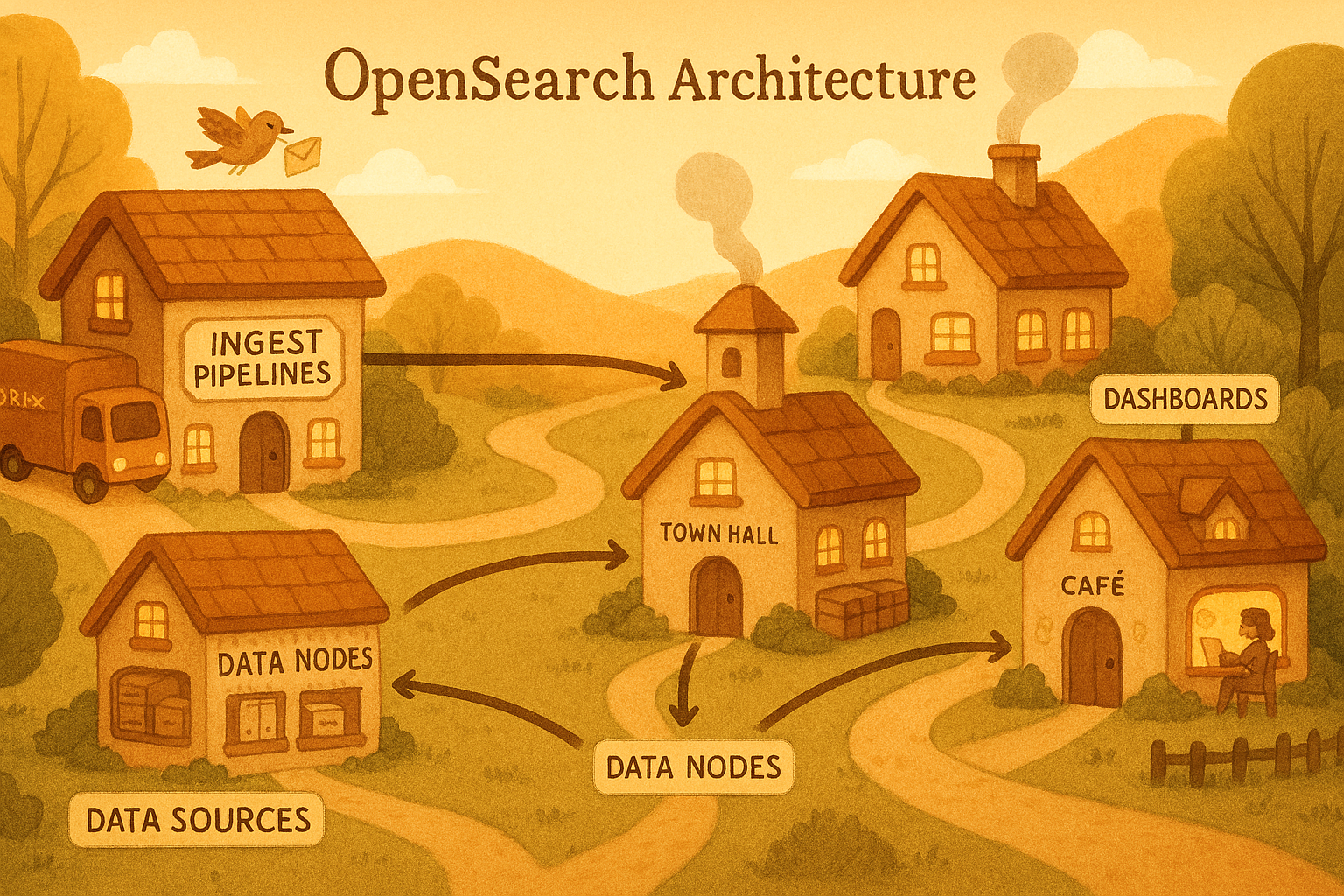
In Part 1 we traced the journey of a log record from logger.info() inside your application, through Python’s logging internals, through Docker’s log driver, and into a Fluent Bit sidecar’s output q...
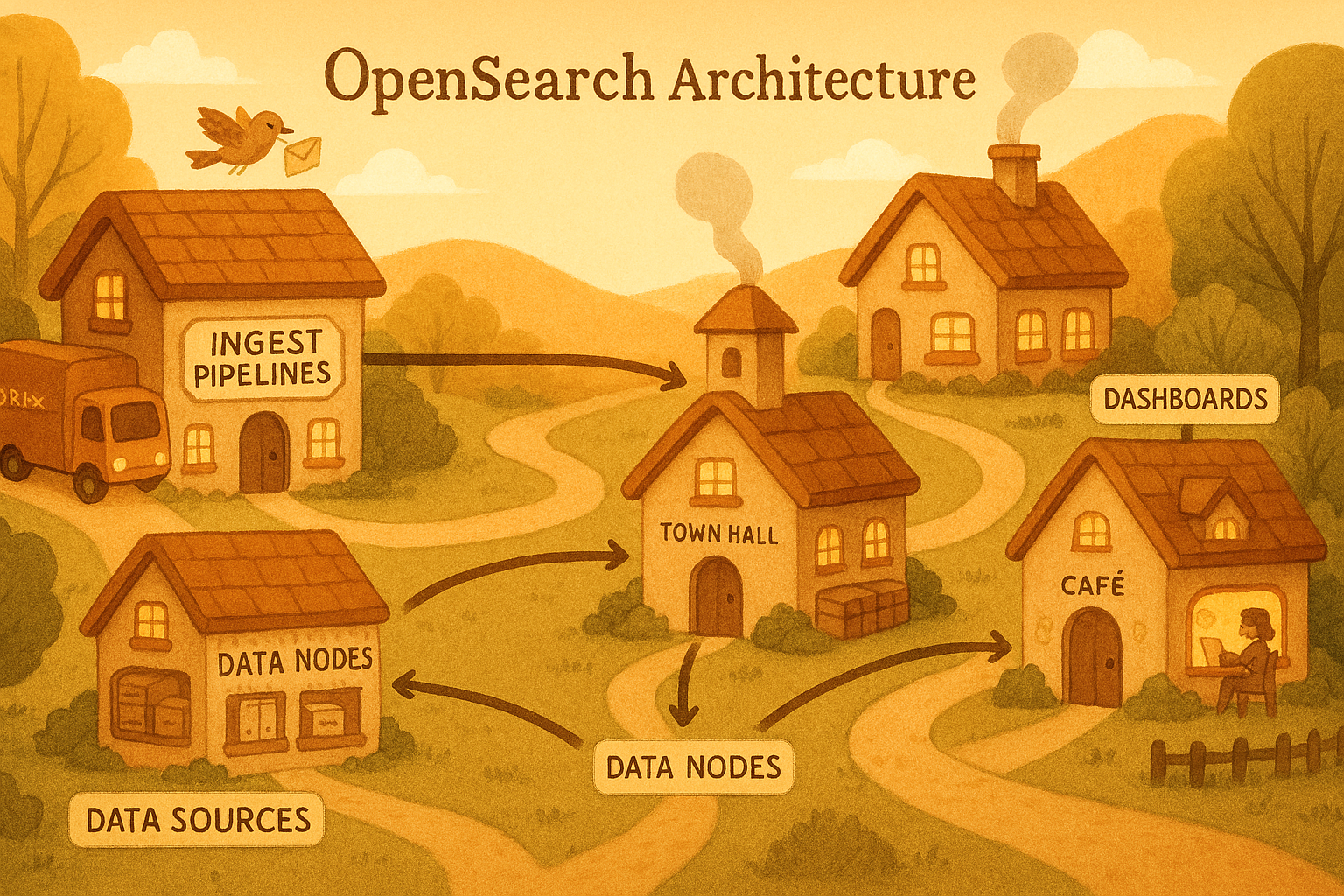
So far in this series we have explored how OpenSearch indexes application data and how reindexing works under the hood. Both posts dealt with data you intentionally write — product catalogs, user r...
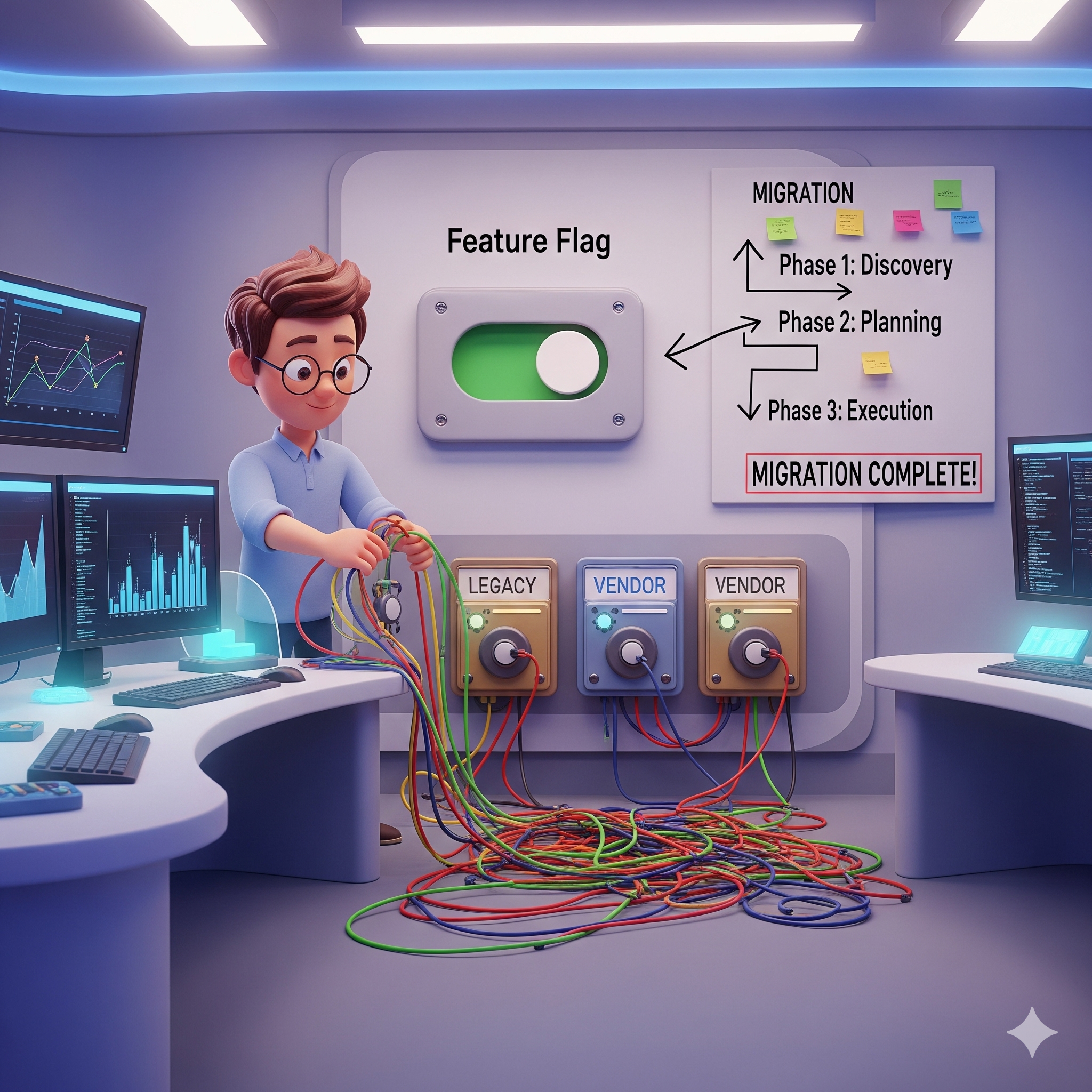
Table of Contents The Setup Case 1: The Zombie Flag Case 2: The Name Collision Nightmare Case 3: The Flag Matrix — When Testing Becomes a Nightmare Looking Back Feature flags feel like...

Table of Contents Introduction The Business Context: Human-in-the-Loop Ingestion The Architecture The Problem: The “Race Condition” Illusion Unmasking the Caches: A Debugging Story Th...

Why OAuth alone can't tell you who a user is, to ID tokens, claims, flows, nonce attacks, UserInfo, SSO, and production-ready Python code.

Beyond the login button — a production-grade breakdown of OAuth 2.0 flows, token mechanics, scope design, and security pitfalls every engineer must know.

In Authentication Deep Dive: How JWT Works we looked at how users authenticate to your application using JWT tokens. The fundamental mechanism there was: prove your identity once (with a password),...